Announcing availability of information protection capabilities to help protect your sensitive data
At the last Microsoft Ignite conference we shared our vision of providing a more integrated and consistent approach to discovering, classifying, labeling and protecting sensitive data. Earlier this year we announced several new capabilities to help you better protect your sensitive information, wherever it lives or travels – across devices, apps, cloud services and on-premises. We remain committed to delivering a comprehensive set of solutions that help you achieve your information security and compliance goals.
This week we’re taking another big step in the journey, with several announcements and updates:
- General availability of centralized management of labels and protection settings in the Security & Compliance Center
- General availability of the Microsoft Information Protection SDK
- Preview of labeling functionality in Word, PowerPoint, Excel and Outlook on Mac
- Preview of labeling in Word and PowerPoint on iOS and Android
- Endpoint protection based on sensitivity labels using Windows Information Protection (coming October 2018)
- Preview of viewing labeled and protected PDFs in Adobe Acrobat Reader on Windows
- Preview of Information Protection analytics
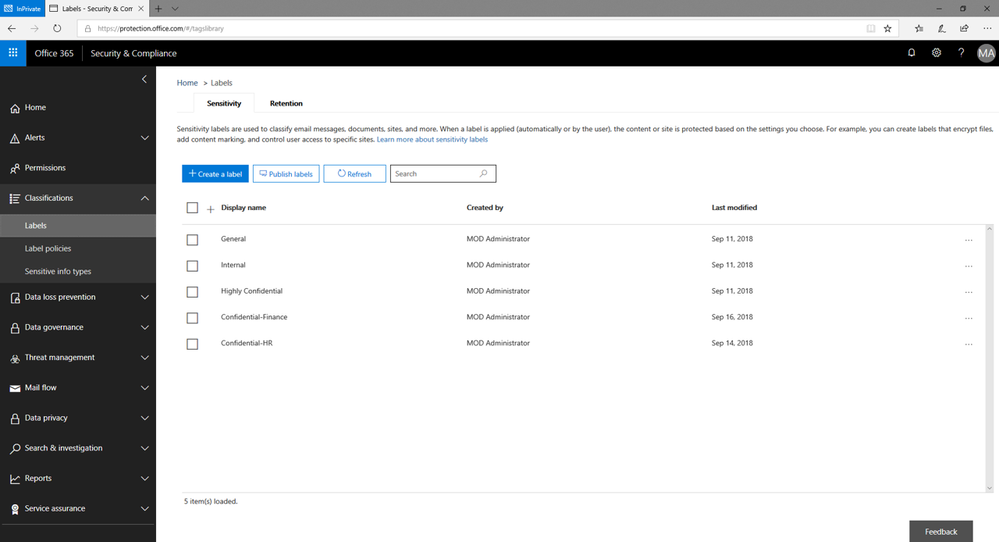
Unified labeling and protection management across Azure Information Protection and Office 365
The new unified labeling experience in the Security & Compliance Center provides a single destination to configure labels and protection policies across Azure Information Protection and Office 365. Today we’re announcing the general availability of this experience – with even more capabilities coming over time. You can create new labels along with policy settings, such as adding encryption and access restrictions, adding visual markings such as watermarks or headers/footers, and controlling external access to labeled sites and groups. These labels can be used by Azure Information Protection, Office apps and Office 365 services. For Azure Information Protection customers, you will be able to use your labels in the Security and Compliance center, and your labels will be synchronized with the Azure portal in case you choose to perform additional or advanced configuration. Learn more about the unified labeling experience and how current Azure Information Protection customers can migrate to the unified labeling experience in our Tech Community blog.
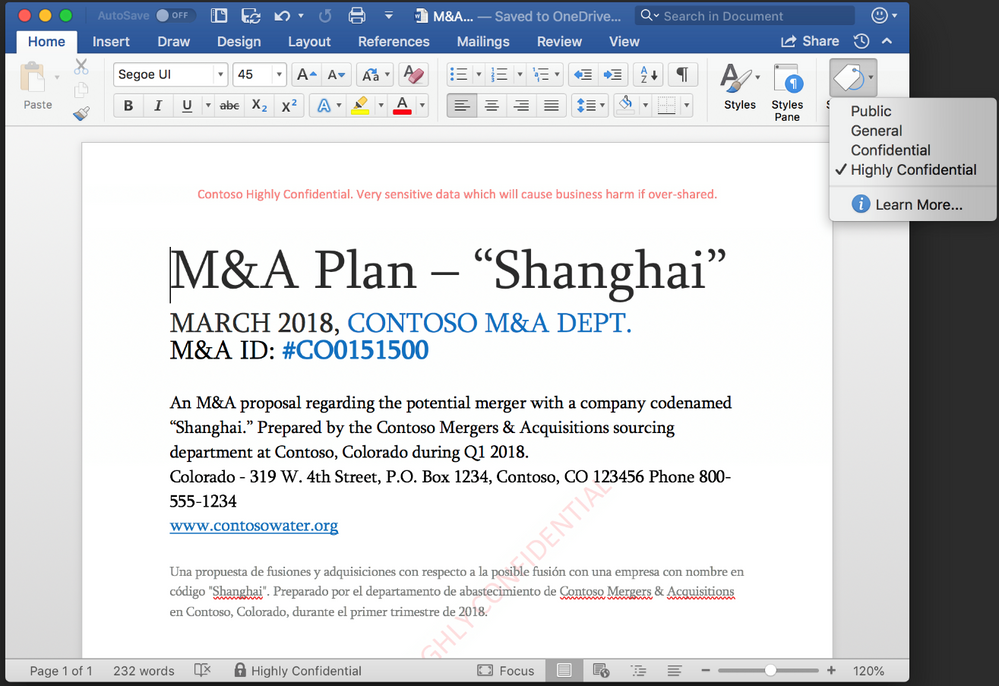
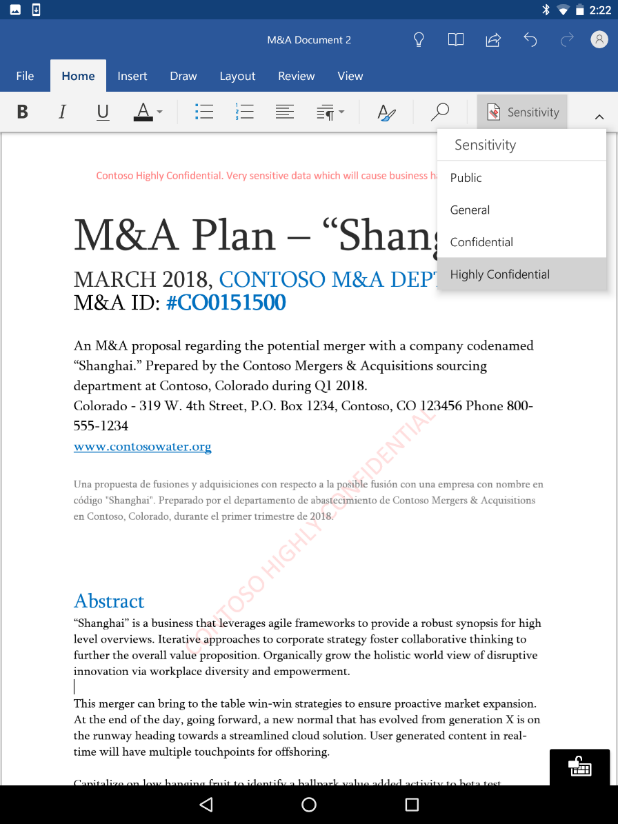
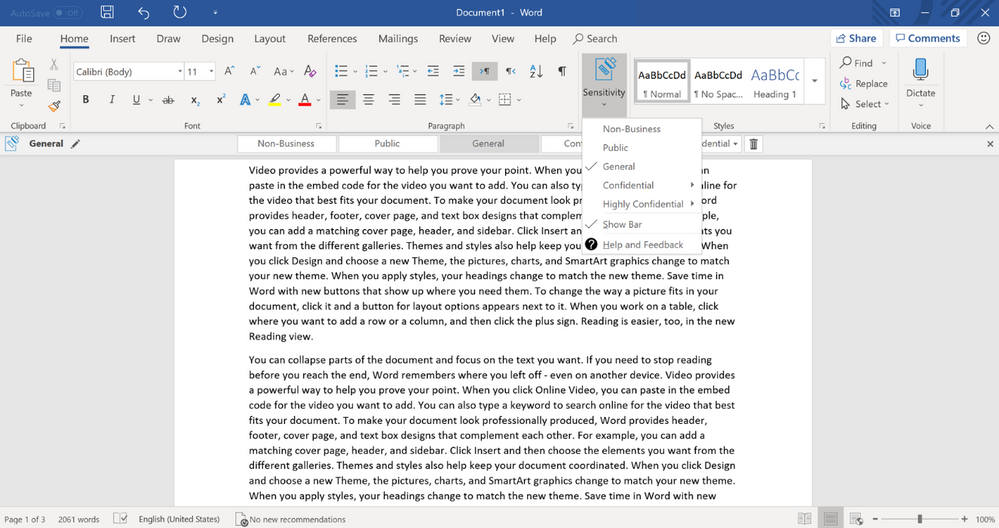
Labeling experiences built natively into Office apps
We also want to make it easy and intuitive for users to protect sensitive information – as they are creating or editing documents and emails. To help achieve this, we are integrating classification, labeling and protection capabilities natively into the most commonly used productivity apps and services. Today we’re announcing the start of the public preview (available to Office Insider program participants) of native labeling capabilities in Office apps across platforms, including Mac (Word, PowerPoint, Excel), iOS (Word, PowerPoint) and Android (Word, PowerPoint). These new capabilities enable preview end-users to apply labels and protection to documents and emails – in a familiar manner, similar to what they’re already experiencing if they’re using the Azure Information Protection client on Windows. For example, if working on a Word document on a Mac device, users can choose the appropriate sensitivity label, such as “Highly Confidential”, and protection settings will be applied to the document automatically – based on the company’s label policy. Learn more about the supported Office applications in our documentation. (Note on preview availability: Word and PowerPoint on iOS and Android are scheduled to be available to Office Insiders the first week of October)
Azure Information Protection labeling and protection on Windows machines
Today we’re also announcing a new public preview version of the Azure Information Protection client. This preview version of the Azure Information Protection client supports the new unified labeling experiences described earlier. Customers using the new unified label management in the Security & Compliance Center can use this preview client to manually label and protect documents in Office apps on Windows – Word, Excel, PowerPoint and Outlook. This version also supports default labeling, mandatory labeling and visual markings (headers, footers and watermarks). The general availability (GA) release is targeting Q1 CY2019 and is planned to also support automatic classification, multilanguage, the viewer, right-click actions from File Explorer and PowerShell scripting.
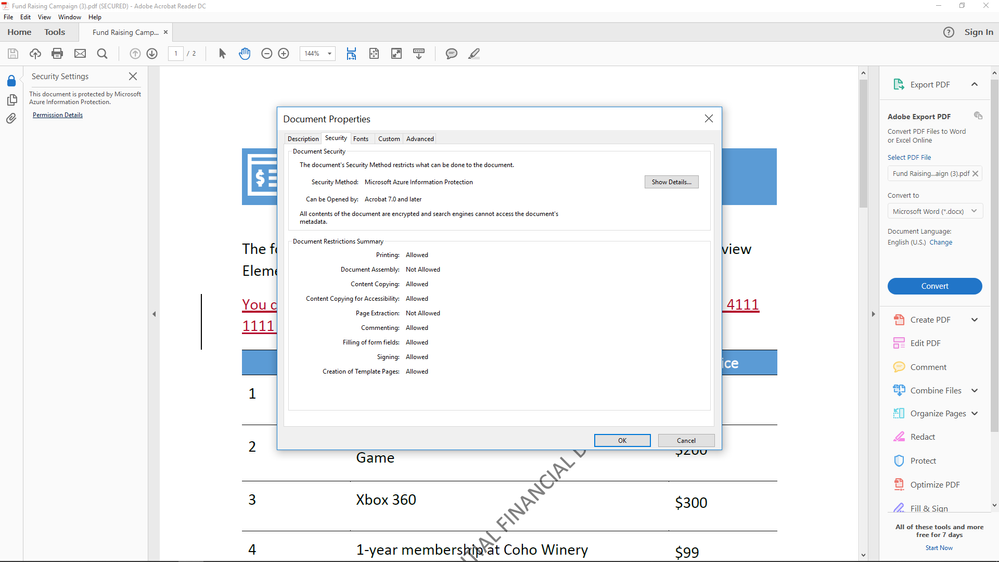
View labeled and protected PDFs with Adobe, our preferred PDF provider for Microsoft Information Protection solutions
For 25 years, Adobe has been the leader in PDF – this makes them a natural fit to be our preferred PDF provider for Microsoft Information Protection solutions. In a few weeks, Adobe will be releasing a public preview of a plug-in to view labeled and protected PDFs directly within Adobe Acrobat Reader on Windows, with support for Acrobat DC and other platforms coming later in the year.
Building native labeling capabilities directly into Office apps across the major device platforms helps broaden the coverage of information protection across your environment, and our goal is to also enable other common productivity apps to integrate our labeling capabilities directly into their own apps and services. This will make it even easier for end-users to work with PDFs that contain sensitive information – they can use the familiar Adobe Acrobat experience to view labeled and protected PDFs, without needing a special viewer application. With the preview, you can get started using the Azure Information Protection client and Azure Information Protection scanner to label and protect PDFs in a manner that can be opened by Adobe Acrobat Reader. In the future we plan to enable our other Information Protection solutions to also label and protect PDFs that can be opened by Acrobat. Learn more about our integration with Adobe Acrobat in our Tech Community blog.
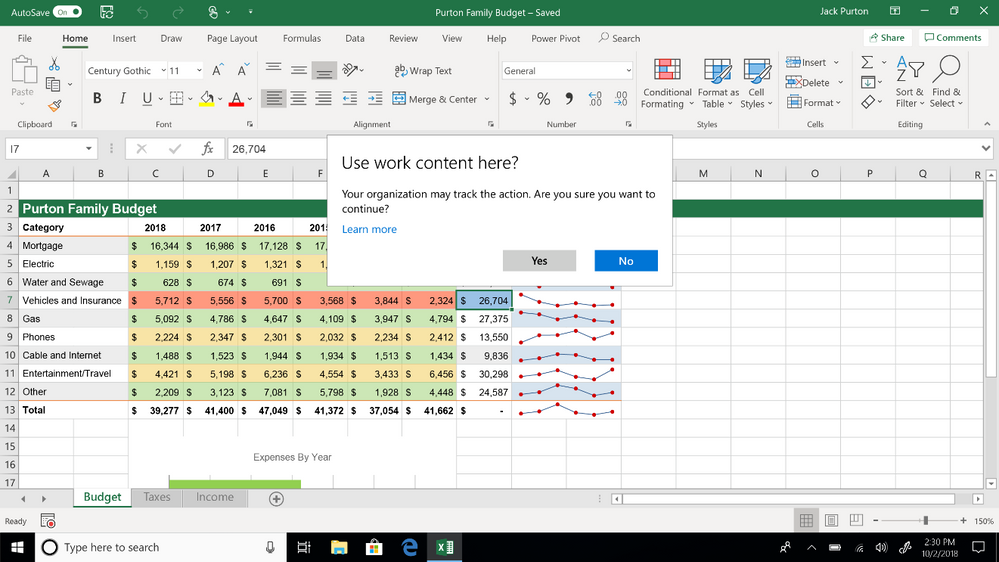
Extend information protection to Windows 10 endpoints
As part of the unified labeling and protection experience, our goal is to ensure that our broad set of information protection solutions can understand labels attached to documents and emails and apply the appropriate policy-based actions. Today we’re announcing that Windows will be able to read, understand and act on sensitivity labels in documents and automatically apply Windows Information Protection (WIP) on work data, no matter how it reaches a managed PC. This extends information protection on managed Windows devices and endpoints and helps protect labeled files from accidental leakage, with or without applying encryption. For example, Windows can understand that a Word document residing on a user’s machine has a label of “Confidential”, and as a result of the policy defined by the organization, apply WIP policy to prevent the copying or sharing of the data to any non-work location from that device (such as personal email accounts, social channels, etc.). We are targeting enabling this capability for customers in the Windows 10 October 2018 Update. Learn more here.
Extend information protection to non-Microsoft apps and services with the Microsoft Information Protection SDK
Earlier this year we announced the public preview of the Microsoft Information Protection SDK, which enables ISVs and service providers to be able to read and apply unified labels and protection to documents – this is particularly useful for files that are beyond the coverage of our information protection solutions. Today we’re announcing the general availability of the SDK for Windows, Mac and Linux – and the public preview of the SDK for iOS and Android. You can get started with all the resources you need here. Using the SDK, you can label and protect content in a way that works with other Microsoft Information Protection apps and services, such as Office apps, Office 365 services, the Azure Information Protection scanner, Microsoft Cloud App Security and several other partner solutions. Learn more about the Microsoft Information Protection SDK on our Tech Community blog.
Proactively protect and control sensitive messages with Office 365 Message Encryption
We also have enhancements to Office 365 Message Encryption that will enable organizations to more easily collaborate on and proactively protect sensitive emails. First, to further support collaboration on protected emails with consumer recipients, Office 365 Message Encryption enables organizations to control whether attachments should also be encrypted with the Encrypt-Only template, which means that recipients retain full permissions to share the attachment in the protected email. This update is generally available today. Additional enhancements, such as the ability to protect PDFs and customize branded emails for any recipient, are planned to be delivered by the end of the calendar year.
Second, to help organizations better manage and control sensitive emails, IT Admins can monitor and view reports on encrypted messages to proactively apply policies to sensitive emails based on observed patterns. We are also releasing the ability for admins to revoke encrypted emails sent to consumer email accounts. These are just a few new updates in Office 365 Message Encryption that will be available in preview by the end of October. To learn more about these capabilities and more, read theTech Community blog for details.
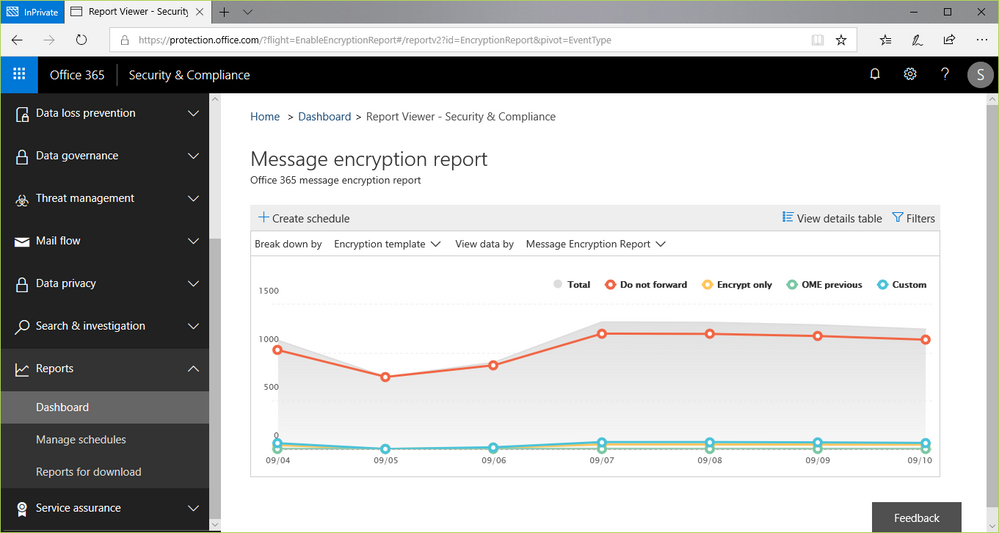
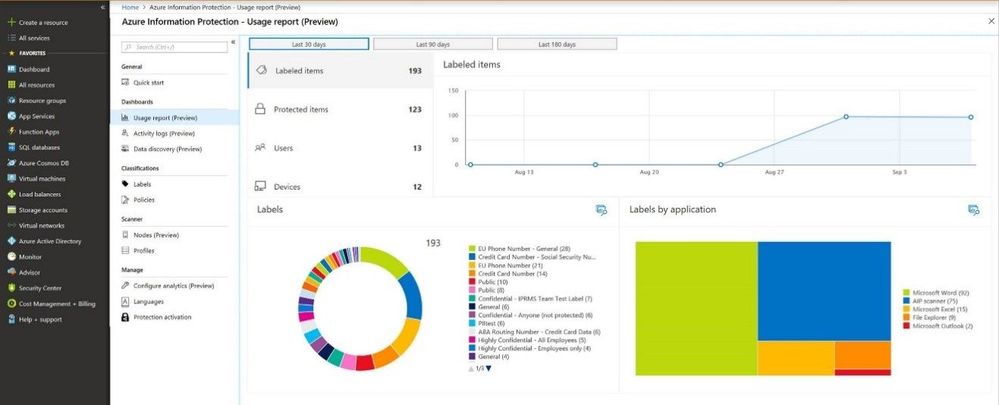
Gain visibility into sensitive data across your organization with Information Protection analytics
The information protection lifecycle wouldn’t be complete without the ability to understand the state of your sensitive data – along with the ability to remediate potential issues. Today we’re announcing the public preview of Azure Information Protection analytics, which gives you insights into labeled and protected documents and emails across your organization. The dashboard provides information on the volume and distribution of files by label type, along with where the label was applied. You can also view details on where sensitive data resides, as well as the specific type of sensitive information contained in files (for example, financial info, PII or other information based on content inspection). Learn more about the Information Protection analytics preview here.
Evaluate sensitive data usage and behavioral access activity to help identify advanced threats
Customers also want the ability to quickly identify advanced threats to their sensitive data – and be able to defend their digital estate against evolving cyber threats. Today we’re announcing the public preview of Information Protection alerts, which helps customers detect advanced data-related attacks and insider threats. The new alerts leverage our advanced machine learning engine to profile the behavior of users accessing and working with sensitive information – based on classification and labeling applied to files by Azure Information Protection. Alerts can be accessed using the Microsoft Graph Security API, or you can stream alerts (using Azure Monitor) to a SIEM solution, such as Splunk and IBM Qradar. Learn more about the Microsoft Graph Security API and get started by reading our blog.
Getting started
Regardless of where you are in your information protection journey, there’s plenty to explore and start implementing – including the new capabilities described here. If you’re an Azure Information Protection customer or Office 365 customer (with an E3 or E5 plan), start using the unified labeling experience in the Security & Compliance center to create, update or modify your sensitivity labels. Start using the Office apps in preview for Mac, iOS and Android to enable preview users to label their documents and emails. Enable your Windows users to do the same by downloading the preview Azure Information Protection client. Beyond Office files, enable users Gain visibility into sensitive data across your organization with the Azure Information Protection analytics preview. Finally, if you use products or services from one of our ISV partners, connect with them for a demo or preview of their integrated functionality.
You can also engage with us and the community on Yammer or Twitter and provide additional feedback on UserVoice.
- Start a trial of EMS and Office 365 E5 to explore the capabilities
- Learn more about Information Protection
- Go deeper and learn more in the Azure Information Protection technical documentation
Source: EM+S Blog Feed