Microsoft Cloud App Security and Windows Defender ATP – better together
Based on our findings, enterprises today have an average of 1,100 cloud applications in their organization, with IT unaware of 61% of the cloud services that users access.
Sourcing from a cloud app catalog of more than 16,000 applications, Discovery in Microsoft Cloud App Security (MCAS), Microsoft Cloud Access Security Broker (CASB) solution identifies the cloud apps that are being used in your organization, provides risk assessments, ongoing analytics and lifecycle management capabilities to control the use.
Microsoft Cloud App Security now uniquely integrates with Windows Defender Advanced Threat Protection (ATP) to enhance the Discovery of Shadow IT in your organization and extend it beyond your corporate network. Our CASB can now leverage the traffic information collected by the Windows Defender ATP, no matter which network users are accessing cloud apps from. This seamless integration does not require any additional deployment and gives admins a more complete view of cloud app- and services usage in their organization.
Integration Highlights
- Discovery of cloud apps beyond the corporate network from any Windows 10 machine
- Single-click enablement
- Machine-based Discovery
- Deep dive investigation in Windows Defender ATP
How it works
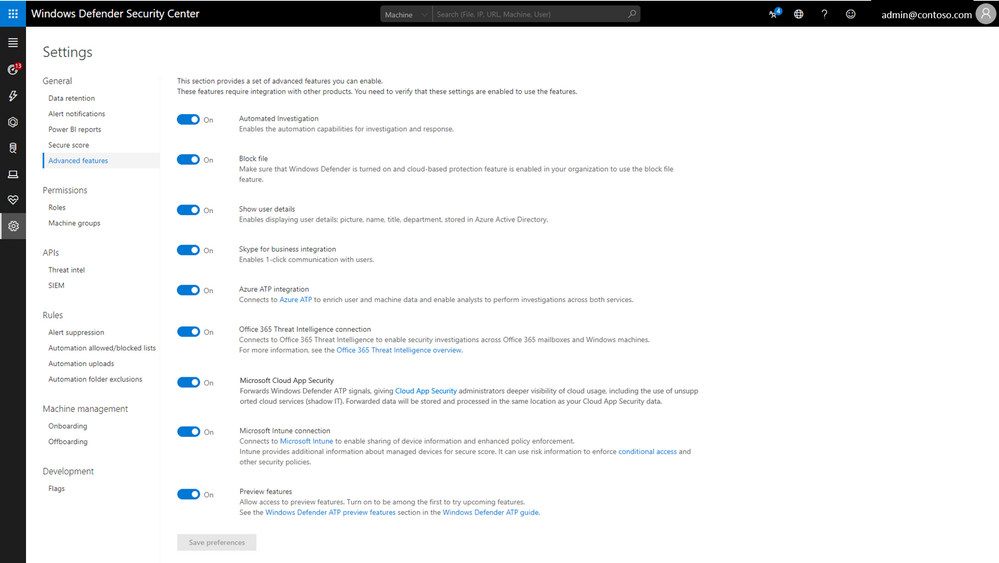
Windows Defender ATP is an integrated part of Windows 10 Enterprise E5. To leverage the existing sensors and send traffic information to Microsoft Cloud App Security, you need to enable this integration via a simple toggle in the Windows Defender Security Center. Windows Defender ATP will then continuously log resource usage from all Windows 10 machines that are onboarded to the service, and report it back to Microsoft Cloud App Security, with signals shared via the Microsoft Intelligent Security Graph.
To get started, admins can go to the Advanced settings page in the Windows Defender Security Center. All you need to do, is activate a single button to enable the connection – and MCAS will start pulling the information immediately.
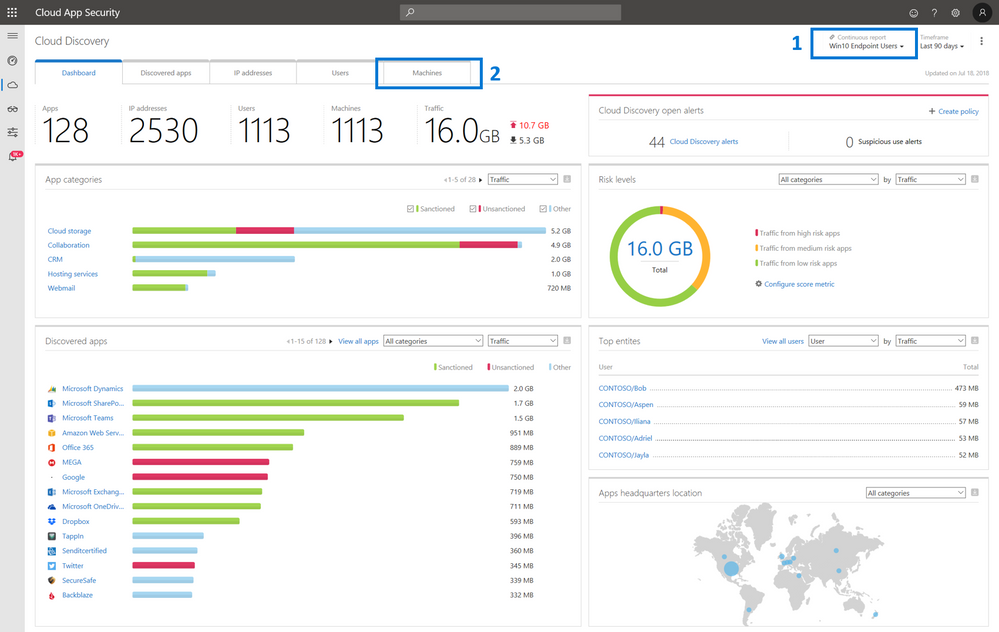
Microsoft Cloud App Security will then leverage the traffic information from Windows Defender ATP’s log store to surface all relevant details in the Discovery Dashboard and provide relevant insights for discovered apps, users, IP addresses and a new, machine-centric view.
Admins now have visibility into the cloud apps that are being accessed, no matter which network the devices are logged into. Furthermore, admins will be able to see how many and which devices are accessing each one of the apps that are discovered.
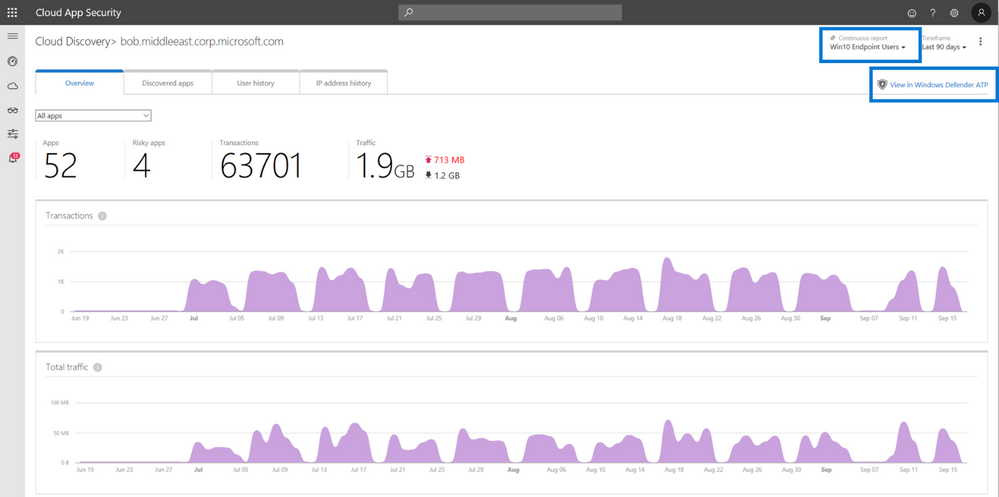
Given the native integration of these products, admins can easily pivot between the two portals. In Image 3 the admin is investigating the usage details of a cloud storage app. To investigate an individual machine with particularly high traffic for this app in more detail, admins can leverage the Windows Defender ATP deep-link within MCAS to navigate directly to the machine investigation in Windows Defender ATP and continue there.
Enabling this seamless Cloud App Discovery experience in Microsoft Cloud App Security is the first step in creating a sophisticated lifecycle management approach to help ensure that your organization securely accesses cloud apps and services. Leverage the breadth of capabilities to identify which apps are being used in your organization, assess their potential risk and enable continuous monitoring to take immediate action when new cloud apps are discovered.
In the near future we will be adding more capabilities to this powerful and unique CASB integration, that will allow admins to manage and block unsanctioned applications
More info and feedback
Learn how to get started with Microsoft Cloud App Security with our detailed technical documentation. Don’t have Microsoft Cloud App Security? Start a free trial today!
New to Windows Defender Advanced Threat Protection? Learn more.
As always, we want to hear from you! If you have any suggestions, questions, or comments, please visit us on our Tech Community page.
Source: EM+S Blog Feed