Visibility into network activity with Traffic Analytics – now in public preview
Today, we are announcing the public preview of Traffic Analytics, a cloud-based solution that provides visibility into user and application traffic on your cloud networks.
Traffic Analytics analyzes NSG Flow Logs across Azure regions and equips you with actionable information to optimize workload performance, secure applications and data, audit your organization’s network activity and stay compliant.
With Traffic Analytics, you now can:
-
Gain visibility into network activity across your cloud networks. Solution provides insights on:
- traffic flows across your networks between Azure and Internet, in Azure, public cloud regions, VNETs and subnets.
- inter-relationships between critical business services and applications.
- applications and protocols on your network, without the need for sniffers or dedicated flow collector appliances.
-
Secure your network; Identify threats on your network, such as:
- flows between your VMs and rogue networks.
- network ports open to the Internet.
- applications attempting Internet access.
- anomalous network traffic behavior (e.g. back-end servers attempting connectivity, to servers outside your network etc.)
-
Improve performance of your applications by:
- capacity planning – eliminate issues of over-provisioning or under utilization by monitoring utilization trends of VPN gateways and other services.
- analyzing in-bound and out-bound flows.
- understanding application access patterns (e.g. Where are the users located?, Can application latency be reduced by better workload placement?).
- identification of traffic hotspots.
With this release, Traffic Analytics brings rich flow monitoring capabilities to your Azure cloud that are on-par with capabilities available on campus networks (via NetFlow, IPFIX, sFlow based tools), without the need for packet capture or flow collection appliances.
Get Started
Find out what’s happening on your cloud! Check out the documentation and start using Traffic Analytics on your Azure network.
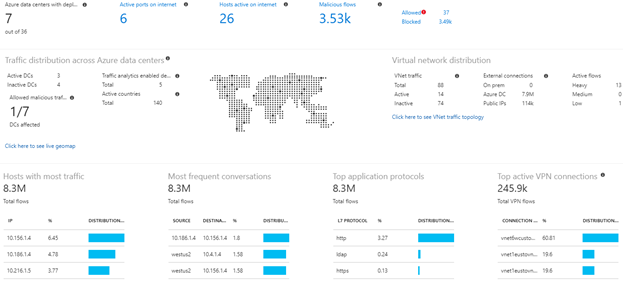
Figure 1: NOC View provides an overview of flows across various regions in Azure.
Figure 2: Geo-map showing traffic across Azure regions. Red dots indicate sources of malicious traffic.
Figure 3: VNET conversation map, with a summary of communicating countries, data centers, hosts etc.
We are listening
We would love to hear from you. Send us your suggestions via the User Voice page.
Source: Azure Blog Feed